Introduction
Azure Security Engineer Associate (AZ-500) is a practical Azure certification that focuses on real security work, not just theory. It helps you learn how to secure identities, networks, data, and workloads inside Azure in a way that matches how enterprises actually operate. If you already touch Azure resources in your job, this certification can quickly improve how you build and protect cloud systems. This guide is written to help engineers and managers understand what AZ-500 is, who it is for, how to prepare, and what to do next after passing.
What is Azure Security Engineer Associate (AZ-500)?
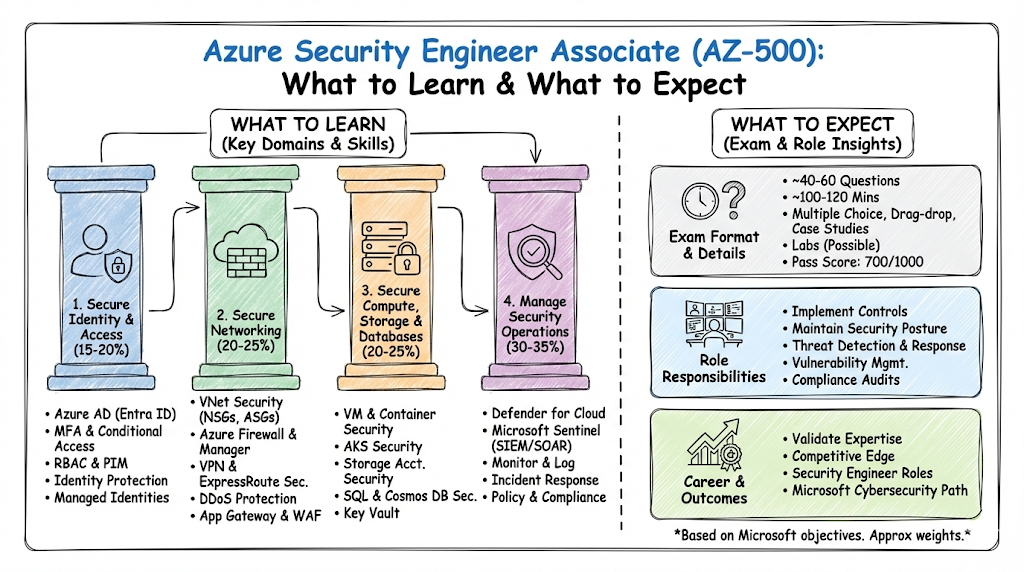
AZ-500 validates your ability to implement and manage security controls across Azure services in real environments. It covers identity and access management, network security, data protection, and security monitoring. This certification expects you to understand why a control is used and how it impacts real workloads. It is especially useful for people who want to work on secure cloud deployment and operational security in Azure.
Who Should Take AZ-500?
AZ-500 is best for working professionals who already use Azure or want to move into cloud security roles. It fits engineers who configure Azure resources and want to ensure security is built correctly from day one. It also suits security engineers moving from on-prem environments to cloud security responsibilities. Managers can benefit too, because it helps them review designs and guide teams with stronger security decisions.
Why AZ-500 Matters in Real Jobs
Most cloud security issues happen because of simple mistakes like too much access, exposed networks, weak secrets handling, or missing logs. AZ-500 teaches you how to prevent these issues using practical controls and correct configuration habits. It also helps you improve security posture in a way that does not slow down engineering teams. Over time, these skills make you trusted for bigger projects, compliance-heavy work, and security-sensitive environments.
Certification Map Table (Track, Level, Order, and More)
This table lists certifications that commonly pair well with AZ-500 in Azure and Microsoft security career paths. Only the AZ-500 link is included because it was provided in your prompt. All other links are marked Not provided to avoid external links.
| Certification | Track | Level | Who it’s for | Prerequisites | Skills covered | Recommended order |
|---|---|---|---|---|---|---|
| AZ-500 Azure Security Engineer Associate | Security / Azure | Associate | Engineers securing Azure identities, networks, workloads, data | Azure basics, IAM basics, networking basics | Identity & access, network security, data protection, monitoring | 1 (Security specialization) |
| AZ-900 Azure Fundamentals | Azure | Fundamentals | Beginners entering Azure | None | Core services, pricing, governance basics | Before AZ-104 / AZ-500 (optional) |
| AZ-104 Azure Administrator Associate | Azure | Associate | Engineers managing Azure resources | Azure basics | Compute, storage, networking, identity, operations | Often before AZ-500 |
| AZ-305 Azure Solutions Architect Expert | Architecture | Expert | Architects designing enterprise Azure solutions | Strong Azure admin + design exposure | Architecture, governance patterns, identity, networking | After AZ-104 (and optional after AZ-500) |
| SC-900 Security, Compliance, Identity Fundamentals | Security | Fundamentals | Beginners entering Microsoft security | None | Security basics, compliance concepts, identity basics | Before SC series (optional) |
| SC-200 Security Operations Analyst Associate | SecOps | Associate | SOC / defenders using Microsoft tools | Security fundamentals helpful | Threat detection, incident response | After AZ-500 or alongside |
| SC-300 Identity and Access Administrator Associate | Identity | Associate | IAM specialists working with Microsoft identity | Identity basics | Identity governance, access control | Before/After AZ-500 |
| SC-400 Information Protection Administrator Associate | Data Protection | Associate | Engineers protecting data and compliance | Security basics helpful | Information protection, governance | After AZ-500 for data-heavy roles |
AZ-500 Mini-Sections (Consistent Format)
What it is
Azure Security Engineer Associate (AZ-500) is a hands-on certification focused on securing Azure environments end-to-end. It checks your ability to implement controls for identities, networks, data, and monitoring. It is designed for real security implementation, not only policy and theory. If your role touches production Azure workloads, this certification maps well to daily responsibilities.
Who should take it
- Cloud engineers who want to add strong security skills to their Azure work and get better at secure configuration
- Security engineers who are moving into Azure and want a structured path to cloud security implementation
- DevOps, Platform, and SRE engineers who manage access, pipelines, and infrastructure and want safer patterns
- Managers who review cloud designs and want deeper practical understanding of risk, controls, and posture
Skills you’ll gain
- Identity and access control design with least privilege thinking and better permission structure
- Practical security configuration across core Azure areas like network access boundaries and workload hardening
- Data protection habits including secure access patterns, encryption awareness, and secrets handling basics
- Monitoring and alerting mindset so you can detect issues early and reduce incident time
- Security posture improvement thinking so you can find gaps, prioritize fixes, and reduce risk steadily
- Stronger ability to explain security trade-offs clearly to teammates, reviewers, and leadership
Real-world projects you should be able to do after it
- Build a secure Azure baseline for a new project that includes safe access rules and deployment guardrails
- Implement least privilege permissions for different teams and environments without blocking delivery
- Secure network connectivity patterns with segmentation and controlled inbound and outbound paths
- Protect storage access and data handling workflows so data is not exposed accidentally
- Set up monitoring signals and alerting patterns that reduce noise but catch real threats
- Create a “secure before production” checklist that teams can follow for repeatable secure releases
Preparation plan (7–14 days / 30 days / 60 days)
7–14 Days Plan (Fast-Track)
- Day 1–2: Understand AZ-500 exam domains, note weak areas, collect study notes and lab checklist
- Day 3–5: Focus on Identity & Access (RBAC basics, least privilege mindset, secure access patterns) + daily practice questions
- Day 6–8: Cover Network Security (segmentation thinking, secure connectivity patterns, safe inbound/outbound controls) + hands-on labs
- Day 9–10: Learn Data Protection (secure storage access, encryption concepts, secrets handling mindset) + scenario practice
- Day 11–12: Do Monitoring & Security Operations (logging signals, alerting, investigation flow) + revision of mistakes
- Day 13–14: Full revision + 2 mock-style practice rounds + fix weak topics + final notes summary
30 Days Plan (Balanced for Working Professionals)
- Week 1: Azure security basics + Identity & Access focus + permission design practice
- Week 2: Network Security deep dive + secure architecture patterns + daily scenario questions
- Week 3: Data Protection + secrets hygiene + secure storage workflows + practice labs
- Week 4: Monitoring & Threat Awareness + full revision + 3 mock rounds + weak-area improvement
- Daily habit: 60–90 minutes study + 20–30 minutes practice questions + short revision notes
60 Days Plan (Strong Foundation + Career Shift Friendly)
- Weeks 1–2: Build Azure base knowledge + security fundamentals + identity basics + small daily labs
- Weeks 3–4: Identity & Access mastery + least privilege patterns + permission review scenarios
- Weeks 5–6: Network Security + segmentation + secure connectivity patterns + workload protection labs
- Weeks 7–8: Data Protection + secure access workflows + monitoring and alerting + investigation practice
- Final 7–10 days: Full revision + multiple mocks + improve weak areas + write a personal “security checklist” for work use
- Weekly habit: 3 days learning, 2 days labs, 1 day revision, 1 day rest or light recap
Common mistakes
- Studying only notes and videos without doing enough hands-on practice and scenario thinking
- Treating identity and access topics as “easy” and then losing marks on permission design questions
- Focusing too much on one area like networking and ignoring monitoring or data protection sections
- Memorizing features without understanding when you should use them and what problem they solve
- Skipping revision until the final days and not tracking weak areas early enough
- Thinking security is a final step instead of building it into design, deployment, and daily operations
Best next certification after this
Option 1: Same Track (Go Deeper in Security)
- SC-200 (Security Operations Analyst) — best if you want SOC-style work, threat detection, incident response, and monitoring-driven security.
- SC-300 (Identity and Access Administrator) — best if you want to specialize in identity governance, access control, and Zero Trust access patterns.
- SC-400 (Information Protection Administrator) — best if your work involves data protection, compliance, and information governance.
Option 2: Cross-Track (Security + Cloud Architecture)
- AZ-305 (Azure Solutions Architect Expert) — best if you want to design secure enterprise architectures and lead cloud design decisions.
- This path fits platform engineers, cloud engineers, and managers who review architecture.
Option 3: Leadership Direction (Security-Aware Engineering Leader)
- Security/Compliance Fundamentals path (SC-900 style) — best if you lead teams and want stronger security + compliance vocabulary for reviews and governance.
- Pair this with architecture thinking and real projects to grow into leadership roles.
Choose Your Path (6 Learning Paths)
This section helps you choose a practical direction after AZ-500. Each path is designed so you can connect certification skills with real work output. Pick one based on the role you want next and the kind of problems you enjoy solving. A clear path helps you avoid collecting random certifications without career impact.
Path 1: DevOps
If you work on building and releasing systems, security must become part of delivery and automation. Focus on safe pipeline access, secrets hygiene, and secure defaults in infrastructure templates. Learn how to reduce risk without slowing down releases. The goal is to ship faster while keeping security stable and repeatable.
Path 2: DevSecOps
This is for engineers who want to embed security into engineering workflows, not keep it separate. Focus on guardrails, repeatable controls, and security checks that run automatically. Improve how you handle permissions, policies, and baseline templates for teams. The goal is to make secure delivery the easiest way to deliver.
Path 3: SRE
SRE needs both reliability and security awareness because incidents often involve access, logs, and monitoring failures. Focus on strong logging signals, alert quality, and safe emergency access patterns. Build incident readiness practices and reduce noisy alerts that hide real threats. The goal is resilient systems with faster detection and recovery.
Path 4: AIOps / MLOps
AIOps and MLOps involve automation and data pipelines, so security becomes identity plus data plus monitoring. Focus on secure access boundaries, secrets handling, and safe automation permissions. Learn how to monitor abnormal activity patterns and protect training or inference workflows. The goal is secure automation that does not create hidden risk.
Path 5: DataOps
DataOps teams need strong control over storage access, sharing patterns, and data movement. Focus on protecting data access paths, encryption awareness, and controlled data exposure. Build a habit of auditing who can access what and why. The goal is useful data systems that remain safe, compliant, and trusted.
Path 6: FinOps
FinOps is about cost clarity and governance, and security impacts cost more than people realize. Focus on preventing misuse, controlling access, and reducing costly mistakes caused by misconfiguration. Learn how governance and security controls reduce financial risk. The goal is stable cloud spending with fewer costly surprises.
Role → Recommended Certifications Mapping
This mapping helps you choose what to learn next based on your current role or the role you want. It focuses on practical growth, not just stacking certificates. Use it as a guide to plan your learning sequence for the next few months. It also helps managers map team learning to real responsibilities.
| Role | Why AZ-500 helps | Recommended next certifications (examples) |
|---|---|---|
| DevOps Engineer | Better secure delivery, safer pipelines, stronger access control | AZ-104, then architecture or security specialization track |
| SRE | Better monitoring signals, safer incident access, improved posture thinking | AZ-104, then security ops or architecture direction |
| Platform Engineer | Stronger guardrails for shared platforms and multi-team environments | AZ-104, then AZ-305 style path + identity depth |
| Cloud Engineer | Safer cloud configuration and stronger risk reduction habits | AZ-104, then AZ-305 or deeper security specialization |
| Security Engineer | Direct match to Azure security implementation responsibilities | Security operations, identity, and data protection paths |
| Data Engineer | Protect storage access and reduce data exposure risk | Data-focused path + data protection specialization |
| FinOps Practitioner | Better governance thinking to reduce cost impact of misuse | Governance + access control awareness + leadership basics |
| Engineering Manager | Better design reviews, risk thinking, and secure decision-making | Architecture direction + security fundamentals for leadership |
Next Certifications to Take (3 Options)
Option 1: Same track (deeper security)
Choose this if you want to become a dedicated cloud security specialist and work directly on security posture and controls. This path is strong for security engineer roles and compliance-heavy projects. It also helps if your team expects you to lead cloud security implementation. Over time, it builds a strong “security-first engineer” profile.
Option 2: Cross-track (security + architecture)
Choose this if you want senior cloud roles where you design systems that must be secure by default. Security plus architecture makes you valuable because you can prevent issues at design time instead of fixing them later. This path fits platform, cloud engineering, and technical leadership roles well. It also prepares you to guide teams on secure patterns and trade-offs.
Option 3: Leadership (security-aware engineering leadership)
Choose this if you manage teams or want to grow into leadership soon. Your goal is to guide secure delivery, approve designs, and ask the right security questions early. This path helps you set expectations, reduce risk in projects, and build good security culture. It is especially useful for managers responsible for reliability and compliance outcomes.
Top Institutions for Training cum Certifications Support (3–4 lines each)
DevOpsSchool
DevOpsSchool provides structured training that fits working engineers who want clarity and real-world mapping, not just exam notes. The learning style focuses on practical understanding, scenario thinking, and hands-on guidance to build confidence. It can support candidates who want a guided plan, consistent practice, and career-focused direction.
Cotocus
Cotocus supports learners who want a clear learning flow with job-aligned skills, especially for modern cloud and engineering roles. It is useful when you want structured guidance and a practical view of how certification learning connects to real work. Many learners prefer it for step-by-step support and direction on what to learn next. It suits engineers who want both preparation and career clarity.
Scmgalaxy
Scmgalaxy is a known name in engineering enablement and can be helpful for learners looking for broad skill coverage. It supports professionals who want structured preparation with an understanding of tools, processes, and delivery environments. It can fit engineers who want more context beyond the exam and prefer learning with real-world examples. It is often considered by people who want practical workplace readiness.
BestDevOps
BestDevOps is helpful for professionals who want practical, industry-aligned guidance for modern engineering paths. It fits people who want preparation support while also understanding how real teams operate in production. It can be useful when you want focused learning plus a broader view of career direction. It suits learners who want to connect security concepts to real delivery work.
devsecopsschool.com
devsecopsschool.com aligns well with engineers who want to embed security into delivery workflows. It fits candidates who want practical DevSecOps thinking like guardrails, secure pipelines, and repeatable controls. It is useful when your goal is to reduce security risk without slowing down development teams. It supports the mindset of building security into everyday engineering work.
sreschool.com
sreschool.com fits reliability-focused learners who want stronger operational discipline with security awareness. It supports SRE-style thinking around monitoring signals, incident response readiness, and safe access patterns. It is useful for engineers who support production systems and want fewer surprises during outages. It helps you balance uptime goals with strong security practices.
aiopsschool.com
aiopsschool.com supports learners exploring automation-driven operations and intelligent monitoring workflows. It fits engineers who want to combine monitoring signals, automation, and cloud operations with security awareness. It can be helpful when your work involves scaling operations and reducing manual intervention safely. It supports a practical approach to modern operational engineering.
dataopsschool.com
dataopsschool.com is relevant for teams building reliable and secure data pipelines and workflows. It supports thinking around repeatable delivery, data quality discipline, and access control awareness. It pairs well with AZ-500 because data security and access patterns are critical in cloud environments. It is useful for data engineers and platform teams managing shared data systems.
finopsschool.com
finopsschool.com supports professionals focused on cloud cost governance, optimization, and financial visibility. It is useful when you want to connect engineering decisions to business outcomes and cost impact. It complements security learning because misuse, misconfiguration, and weak access control often lead to unexpected costs. It helps create a balanced view of governance, cost, and control.
FAQs — Difficulty, Time, Sequence, Value, Career Outcomes
1) Is AZ-500 difficult for beginners?
Yes, it can be challenging if you are completely new to Azure and cloud security basics. However, if you learn Azure identity, networking fundamentals, and common security patterns first, it becomes manageable. The exam becomes easier when you practice scenarios, not just read concepts. A structured plan and hands-on labs reduce difficulty a lot.
2) How much time do I need to prepare?
Most working engineers do well with a 30-day plan when they study consistently and practice weekly. If you are new to Azure security, give yourself 60 days so you can build fundamentals without stress. Fast-track (7–14 days) is only realistic if you already work in Azure security-related tasks. The key is consistency more than long study hours.
3) Do I need AZ-104 before AZ-500?
It is not mandatory, but it helps a lot because AZ-104 builds your Azure administration foundation. When you understand how Azure resources are managed, security controls make more sense. If you already have real Azure experience, you can go directly to AZ-500. If you feel lost in Azure basics, AZ-104 first is a safer route.
4) What is the best order if I want cloud security roles?
A common order is Azure fundamentals → Azure admin basics → Azure security specialization. This order helps you understand what you are securing and why it matters. If you already work with Azure daily, you can shorten the sequence. Your role and current skill level should decide the order, not only a generic roadmap.
5) Does AZ-500 help in salary growth?
It can help, especially when you can show real security work like safer identity design and stronger monitoring. The biggest salary impact comes when certification skills turn into better project outcomes. Many employers value security talent because misconfigurations create high risk. Use small projects and clear documentation to demonstrate your capability.
6) Is AZ-500 useful for DevOps engineers?
Yes, because DevOps engineers often manage access, pipelines, environments, and cloud configuration. AZ-500 improves how you handle least privilege, secrets, and safe network patterns. It also helps you build security into delivery so releases remain fast and safe. This makes you more trusted for production-critical work.
7) Is hands-on practice necessary?
Yes, hands-on practice is essential because the exam is scenario-focused and real-world oriented. Without practice, concepts feel abstract and are easy to confuse. Practice also helps you remember how controls work in real situations. Even small labs or guided exercises can improve your understanding quickly.
8) What job roles benefit most after AZ-500?
Cloud Security Engineer and Security Engineer benefit directly because the skills map to daily tasks. Platform engineers and SREs benefit because they build and run production systems that must be secure. DevOps and cloud engineers benefit because they manage deployment paths and access controls. Managers benefit by making better review decisions and reducing risk in designs.
9) Can managers take AZ-500?
Yes, and it is useful for managers who lead cloud teams or oversee security outcomes. It helps you ask better questions and spot risky design choices early. You do not need to implement every control yourself, but you should understand what good looks like. That awareness improves delivery quality and compliance confidence.
10) What mistakes cause most failures?
Common failures come from skipping practice, ignoring identity topics, and cramming too late. Many people study features but do not understand use-cases and trade-offs. Some focus heavily on networking and forget monitoring and data protection. A weekly revision habit and weak-area tracking prevents these mistakes.
11) How do I prove skills after certification?
The best proof is small, clear projects that demonstrate secure design decisions. Build a secure baseline, implement least privilege, protect storage access, and set up monitoring signals. Then document what you did and why you chose those controls. This creates strong evidence for interviews and internal promotions.
12) What is the best next step after passing?
Pick one direction: deeper security, cross-track architecture, or leadership development. Your next certification should match your target role and the work you want to do daily. Also choose one real project to apply the new skills immediately. That combination turns certification into career momentum.
FAQs — AZ-500 Focused
1) What does AZ-500 mainly test?
It mainly tests your ability to secure Azure in real situations across identity, network, data, and monitoring. The exam expects you to know which control fits which scenario. It also checks if you understand security posture improvement and operational readiness. Think of it as a practical “secure Azure workloads” test.
2) Is AZ-500 more practical or theoretical?
It is more practical because it focuses on implementing controls and understanding how they work. You still need theory, but only to support real decisions. If you study with scenarios, it becomes simpler. If you study only definitions, it becomes confusing.
3) What should I focus on first?
Start with identity and access because it affects almost every security decision in Azure. Learn least privilege thinking and permission structure basics early. Then move to networking and secure connectivity patterns. This creates a strong base for the rest of the topics.
4) How important is networking for AZ-500?
Networking is very important because exposed access paths create major security issues. You should understand segmentation ideas and safe inbound and outbound control thinking. You should also know how network decisions affect workloads. Strong networking security knowledge improves both exam performance and job value.
5) How important is monitoring and logging?
Monitoring and logging are crucial because you cannot defend what you cannot see. AZ-500 expects you to understand security signals and why alerts matter. It also helps you learn how detection improves incident response. This is a key difference between “secure setup” and “secure operations.”
6) Can I prepare only using notes and videos?
Notes and videos help, but they are not enough for most learners. You need practice to understand real configuration choices and scenario thinking. Try to connect each topic to a real “why” and “when.” Even small practical exercises create stronger memory and confidence.
7) How do I avoid last-minute panic?
Use a weekly plan and do small revision cycles instead of leaving everything for the end. Track weak areas early and fix them during the middle of your plan. Do at least one round of exam-style practice before the final week. This keeps your preparation calm and predictable.
8) What is a simple passing strategy?
Understand the core areas, practice realistic scenarios, and revise weak topics early. Use mock-style questions to improve speed and reduce silly mistakes. Focus on identity and networking because they carry heavy practical weight. End your plan with a full revision pass so you feel confident.
Testimonials
Testimonial 1 — Priya
“I was working on Azure resources daily but security always felt confusing and scattered. After preparing for AZ-500, I started designing access properly and stopped giving broad permissions. The biggest change for me was learning to think in real scenarios, not just features. It helped me speak confidently in interviews and in security reviews.”
Testimonial 2 — Ankit
“AZ-500 made me more careful and structured while deploying workloads in Azure. I learned how small misconfigurations can create big risks and how to prevent them early. The preparation plan also helped me stay consistent without burning out. After passing, I got assigned to more critical projects in my team.”
Testimonial 3 — Rahul
“I wanted to move into cloud security but didn’t know where to start. AZ-500 gave me a clear roadmap and practical skills like identity control, monitoring mindset, and safer network patterns. I also built small projects while learning, which became great proof during job discussions. It felt like a real career upgrade, not just an exam.”
Testimonial 4 — Sneha
“As an SRE, I used to focus mainly on uptime and incident response, but AZ-500 improved my security awareness. I learned why logging and alerting matter for security and how to design safer access during incidents. It helped me reduce risk without impacting reliability goals. It also improved collaboration with security teams.”
Testimonial 5 — Karthik
“I was in DevOps and wanted to shift toward DevSecOps. AZ-500 helped me understand identity and network security in a practical way that fits pipelines and deployments. I started applying secure defaults and improved secrets handling in our workflows. This certification gave me both confidence and clear next steps.”
Conclusion
AZ-500 is valuable because it improves how you secure Azure systems in practical, job-relevant ways. It trains you to think clearly about identity access, network exposure, data protection, and monitoring signals, which are the areas where real cloud risks often appear. The best results come when you combine study with small hands-on projects and document what you implemented and why. After passing, choose a clear path—security depth, architecture growth, or leadership readiness—so your next steps match your target role and not just your resume. When you apply these skills consistently, you build trust, reduce risk, and become a stronger engineer for real production environments.