Introduction
Kubernetes has completely changed how we build and scale software. Today, it is the engine powering modern technology teams worldwide. But there is a catch: running applications at this massive scale creates complex security challenges. Companies are deploying code faster than ever, yet they are struggling to keep hackers out. Having spent years building, breaking, and securing infrastructure, I can tell you that container security is the most highly demanded skill in the market today. That is exactly why the Certified Kubernetes Security Specialist (CKS) certification is so valuable. Let’s dive into everything you need to know about the CKS, from the skills you will learn to how you can easily prepare for the exam.
Certification Overview & Quick Facts
| Certification | Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
|---|---|---|---|---|---|---|
| CKA | Admin | Intermediate | System Admins, DevOps Engineers | None | Cluster setup, networking, storage, troubleshooting | 1 |
| CKS | Security | Advanced | Security Engineers, DevSecOps, SREs | Active CKA Certification | Cluster hardening, supply chain security, runtime security | 2 |
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
The Certified Kubernetes Security Specialist (CKS) is an advanced, performance-based certification. It tests your hands-on ability to secure container-based applications and Kubernetes platforms during the build, deployment, and runtime phases in simulated, real-world environments.
Who should take it
This certification is designed for working engineers and managers who already understand how Kubernetes operates and want to specialize in securing it. You should take this if you are a DevOps Engineer, DevSecOps professional, Site Reliability Engineer (SRE), or a Security Engineer looking to validate your cloud-native security skills to global employers.
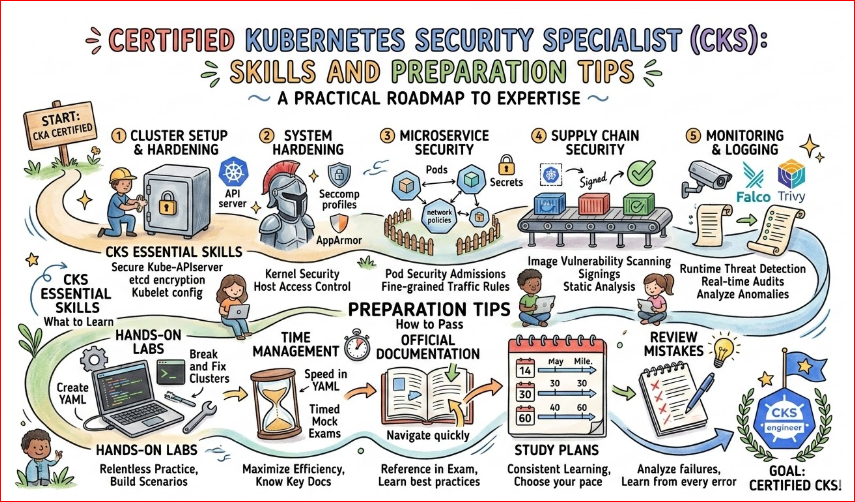
Skills you’ll gain
- Cluster Setup and Hardening: Restricting access to the API server, configuring Role-Based Access Control (RBAC), and securing the etcd datastore.
- System Hardening: Minimizing host OS footprints, configuring AppArmor/seccomp profiles, and securing IAM roles.
- Microservice Vulnerability Minimization: Managing Kubernetes secrets, implementing pod security standards, and handling mTLS.
- Supply Chain Security: Image scanning, securing base images, and signing container images.
- Monitoring, Logging, and Runtime Security: Detecting malicious activities, configuring audit logs, and utilizing tools like Falco and Trivy.
Real-world projects you should be able to do after it
- Build a fully automated container image vulnerability scanning pipeline in your CI/CD process.
- Implement strict Network Policies that isolate tenant namespaces in a multi-tenant cluster.
- Configure runtime threat detection to automatically alert engineering teams if a container’s shell is accessed.
- Audit and remediate an existing production Kubernetes cluster to pass compliance and security benchmarks.
Preparation Plan
Your study timeline depends heavily on your current daily exposure to Kubernetes. Here is how I recommend structuring your time:
- The 7–14 Days Plan (The Sprinter): This is only for engineers who manage secure Kubernetes clusters daily. Spend 2-3 hours a day purely on practice exams and simulating the testing environment. Focus strictly on speed, as time management is the biggest hurdle.
- The 30 Days Plan (The Focused Engineer): Dedicate 1.5 to 2 hours every weekday and 4 hours on weekends. Spend the first two weeks reviewing the core domains (Supply Chain, Runtime, Hardening). Spend the last two weeks taking timed mock exams and mastering imperative commands.
- The 60 Days Plan (The Steady Learner): Ideal for busy managers or engineers who touch K8s occasionally. Study 1 hour a day. Take one week per exam domain. Build a homelab or use cloud credits to break and fix clusters. Save the last three weeks entirely for hands-on labs and speed drills.
Common mistakes
- Ignoring the Prerequisite: Forgetting that your Certified Kubernetes Administrator (CKA) certification must be active on the day you take the CKS.
- Memorizing instead of doing: The exam is 100% practical. Reading books won’t help if you can’t type
kubectlcommands and edit YAML files quickly invim. - Poor time management: Getting stuck on a 4% weighted question for 20 minutes and failing to reach the easier, high-weighted questions at the end of the exam.
- Not knowing the official documentation: You are allowed to use specific official docs during the exam. Failing to know exactly where to search for snippets (like AppArmor profiles or Seccomp configurations) will cost you precious time.
Next certifications to take
Once you conquer the CKS, your learning journey doesn’t stop. Depending on your career goals, here are three directions you can take:
- Same Track (Deep Technical): Advanced vendor-specific security certs (e.g., specialized service mesh or eBPF security training).
- Cross-Track (Broadening Scope): Cloud-specific security certifications (e.g., AWS Certified Security – Specialty or Azure Security Engineer) to secure the infrastructure surrounding your clusters.
- Leadership (Management Level): Certifications like CISSP or CISM to bridge the gap between technical implementation and enterprise risk management.
Choose Your Path
The beauty of the CKS is that it amplifies your value across multiple technical disciplines. Here are six distinct learning paths and how Kubernetes security fits into them.
DevOps
As a DevOps professional, your primary goal is delivering software rapidly and reliably. Adding the CKS to your path ensures that the CI/CD pipelines you build are not just fast, but secure by default. You will learn to integrate image scanning and policy-as-code into your automated workflows, making security a seamless part of the deployment process rather than a bottleneck.
DevSecOps
If this is your chosen path, the CKS is the holy grail. DevSecOps is all about shifting security left. The CKS directly trains you on supply chain security, ensuring that vulnerabilities are caught before they ever reach the cluster. It proves you can bridge the traditional divide between rapid software development and rigorous information security protocols.
SRE (Site Reliability Engineering)
Reliability and security are deeply intertwined; a compromised system is not a reliable system. For SREs, the CKS path provides the skills to ensure high availability isn’t compromised by bad actors. You will master runtime security, anomaly detection, and cluster hardening, ensuring that your Service Level Objectives (SLOs) are protected from malicious disruptions.
AIOps/MLOps
AI and Machine Learning workloads are increasingly containerized and orchestrated via Kubernetes. Models require massive amounts of data, often sensitive. By taking the CKS path, MLOps engineers learn how to secure the training pipelines, isolate GPU workloads securely, and ensure that data feeds are not exposed through misconfigured Kubernetes manifests.
DataOps
DataOps professionals manage the automated delivery of data across the organization. Because databases, message queues, and streaming platforms (like Kafka) are routinely hosted on Kubernetes, data breaches are a massive risk. The CKS teaches you how to implement strict Network Policies, RBAC, and secrets management to keep data pipelines airtight.
FinOps
FinOps practitioners focus on maximizing the business value of cloud spend. While it seems unrelated to security, misconfigured clusters (like exposed APIs leading to crypto-mining malware) can result in catastrophic cloud bills. Understanding K8s security helps FinOps professionals ensure that resource quotas, limits, and secure access policies are enforced, protecting the company’s bottom line.
Role → Recommended Certifications Mapping
| Job Role | Recommended Certification Sequence | Why This Path Makes Sense |
|---|---|---|
| DevOps Engineer | CKA → CKS | Start with CKA to master operational skills, then add CKS to prove you can build secure infrastructure pipelines. |
| SRE (Site Reliability Engineer) | CKA → Cloud Architect Pro → CKS | CKA is mandatory for K8s operations. Adding CKS ensures runtime security, which directly protects system uptime and reliability. |
| Platform Engineer | CKA → CKAD → CKS | You are building the internal developer platform. CKS ensures the environments you provide to developers are secure by design. |
| Cloud Engineer | Cloud Associate → Cloud Pro → CKA → CKS | Essential if you manage hosted Kubernetes services like EKS, AKS, or GKE, helping you lock down the cloud provider’s network. |
| Security Engineer | Security+ → Cloud Security → CKA → CKS | This specific sequence transforms you into an elite cloud-native security expert capable of defending complex enterprise architectures. |
| Data Engineer | Cloud Data Specialty → CKAD → CKS | Critical if your K8s clusters process highly sensitive data, financial records, or PII that must meet strict compliance laws. |
| FinOps Practitioner | FinOps Certs → Cloud Architect → CKA | Helps you understand how Kubernetes compute resources are billed, so you can prevent costly security breaches like crypto-mining. |
| Engineering Manager | CKA → CKS | CKA helps you understand the daily technical challenges your team faces, while CKS helps you guide enterprise security and compliance strategies. |
Top Institutions for CKS Training & Certification
DevOpsSchool
DevOpsSchool is a premier global training organization recognized for its deeply technical, hands-on approach. They offer highly structured bootcamps designed by industry veterans to take you from a novice to a certified expert. Their CKS program is specifically tailored to real-world scenarios, ensuring you pass the exam and excel at your job.
Cotocus
Cotocus excels at providing customized corporate training and individual upskilling in the cloud-native space. Their curriculum is strictly aligned with the latest CNCF exam updates. They focus heavily on practical labs, ensuring that candidates are comfortable with the fast-paced, command-line-driven nature of the CKS exam.
Scmgalaxy
Known for its massive community and deeply technical forums, Scmgalaxy provides comprehensive training tracks for software configuration management and cloud-native security. Their K8s security modules break down complex concepts like TLS and RBAC into easily digestible, bite-sized lessons perfect for working professionals.
BestDevOps
BestDevOps focuses on the intersection of rapid delivery and robust security. Their training programs are designed for engineers who need to learn how to integrate tools like Trivy, Falco, and OPA Gatekeeper into enterprise environments. Their exam prep simulators are highly rated for mimicking the actual test environment.
devsecopsschool.com
This institution is entirely dedicated to the DevSecOps philosophy. Their CKS training goes beyond just passing the exam; it teaches engineers how to build a culture of security within their organizations. They provide excellent mentoring on supply chain security and container image hardening.
sreschool.com
SREschool focuses on the reliability aspect of infrastructure. They treat K8s security as a core component of system uptime. Their CKS modules are highly recommended for engineers who want to understand how security incidents impact Service Level Indicators (SLIs) and how to automate incident response.
aiopsschool.com
With the rise of AI, aiopsschool.com bridges the gap between machine learning operations and infrastructure management. They offer unique perspectives on how to apply CKS principles to secure distributed AI workloads, ensuring that sensitive training data remains isolated and protected within the cluster.
dataopsschool.com
Focused on the modern data lifecycle, this institution helps data engineers and platform teams understand K8s security. Their CKS training emphasizes securing persistent volumes, managing stateful sets securely, and ensuring that internal data pipelines are immune to unauthorized internal access.
finopsschool.com
Finopsschool.com provides a unique lens on Kubernetes security by tying it to cloud economics. Their training highlights how security breaches lead to financial leaks and how implementing CKS-level system hardening can drastically reduce unwanted compute resource consumption.
Testimonials
“Taking the CKS was the most challenging but rewarding step in my career. The hands-on nature of the exam forced me to actually understand Linux system internals and Kubernetes APIs, rather than just memorizing multiple-choice answers. Shortly after getting certified, I transitioned into a Senior DevSecOps role leading infrastructure security for a major fintech firm in Bengaluru.”
— Rahul M., Senior DevSecOps Engineer
“As an Engineering Manager, I needed to ensure my team wasn’t just deploying fast, but deploying safely. The training and certification path for the CKS gave us a standardized framework for security. Now, security is baked into our deployment pipelines, and our compliance audits are a breeze.”
— Sarah T., VP of Platform Engineering
“I thought I knew Kubernetes well because I had my CKA, but the CKS opened my eyes to how vulnerable an out-of-the-box cluster really is. Learning how to properly implement AppArmor and Falco has completely changed how I architect our production environments.”
— Amit K., Cloud Infrastructure Architect
Frequently Asked Questions (FAQs)
1. Is the CKS certification difficult?
Yes. It is widely considered the most challenging certification in the CNCF catalog. It is 100% performance-based, meaning you must execute tasks in a live command-line environment under a strict time limit. There are no multiple-choice questions to guess on.
2. How much time do I have to complete the exam?
You have exactly 2 hours (120 minutes) to complete 15 to 17 hands-on tasks. Time management is usually the biggest challenge for candidates, which is why practicing with a timer is essential.
3. What are the strict prerequisites for the CKS?
You must hold an active Certified Kubernetes Administrator (CKA) certification on the day you schedule and take the CKS exam. The Certified Kubernetes Application Developer (CKAD) does not fulfill this requirement.
4. Can I take the CKS immediately after the CKA?
Yes, and it is highly recommended. The CKS builds directly on the administrative skills you learn in the CKA. Taking it while the CKA knowledge is still fresh in your mind will drastically reduce your study time.
5. Is the CKS worth it for my career in India and globally?
Absolutely. Cloud-native security is a massive priority for companies worldwide. Having the CKS on your resume immediately flags you to recruiters and engineering managers as a specialized expert, often leading to senior roles and higher compensation brackets.
6. Do I need to be a Linux expert to pass?
You don’t need to be a kernel developer, but you must be very comfortable with Linux command-line operations, editing files using vim or nano, understanding systemd, managing processes, and knowing basic networking concepts.
7. Are we allowed to use the internet during the exam?
You cannot freely browse the internet. However, you are permitted to access specific official documentation, primarily the official Kubernetes docs (kubernetes.io/docs), Trivy docs, Falco docs, and AppArmor docs.
8. How long is the CKS certification valid?
The CKS certification is valid for 24 months from the date you pass the exam. Because Kubernetes security evolves so rapidly, the CNCF requires you to recertify to prove your skills are up to date.
9. What if I fail the exam on my first try?
Don’t panic. A significant number of engineers fail on their first attempt due to the time crunch. Your exam registration usually includes one free retake. Use the failure to understand which domains you need to practice more.
10. Do I need to know how to write code (Java, Python, etc.)?
No. The CKS is an infrastructure and operational security exam. While understanding how applications work helps, you will not be asked to write or debug application source code. You will mostly be writing and editing YAML files and bash commands.
11. Does the exam use a specific cloud provider like AWS or Azure?
No. The exam is completely vendor-neutral. You will be working on vanilla Kubernetes clusters provisioned on Linux virtual machines. The skills you learn are applicable across EKS, AKS, GKE, or on-premise setups.
12. How do I book the exam and get started?
You can view all the official details, requirements, and registration steps directly at the CKS Official Link.
Here are 8 essential Frequently Asked Questions (FAQs) for your blog, written in simple, professional English. They cover the exact details your readers will want to know about difficulty, time, prerequisites, and career value.
Frequently Asked Questions (FAQs)
1. What are the strict prerequisites for taking the CKS?
To take the CKS exam, you must hold an active Certified Kubernetes Administrator (CKA) certification on the day of your test. Please note that the Certified Kubernetes Application Developer (CKAD) certification does not meet this requirement.
2. Is the CKS exam difficult to pass?
Yes, it is widely considered the most challenging certification provided by the Cloud Native Computing Foundation (CNCF). It is 100% performance-based. There are no multiple-choice questions; instead, you must solve real security problems in a live command-line environment under a strict time limit.
3. How much time do I have to complete the exam?
You are given exactly 2 hours (120 minutes) to complete 15 to 17 hands-on tasks. Because the exam is heavily practical, time management is usually the biggest hurdle for candidates. Practicing with a timer beforehand is highly recommended.
4. Is the CKS certification worth it for my career?
Absolutely. As cloud adoption grows in India and globally, companies are urgently looking for engineers who can secure their infrastructure. Holding a CKS certification instantly proves your expertise to recruiters, opening doors to senior roles like Lead DevSecOps Engineer or Cloud Security Architect.
5. How long is the CKS certification valid?
The certification is valid for 24 months (2 years) from the date you pass. Kubernetes security tools and attack vectors evolve very quickly, so the CNCF requires professionals to recertify to ensure their skills remain current.
6. What happens if I fail the exam on my first try?
Do not worry if you do not pass on your first attempt—many experienced engineers face this due to the strict time limit. Your exam registration includes one free retake. You can use your first attempt to understand the exam format and identify which topics need more practice.
7. Do I need to know how to write code to pass?
No, you do not need to be a software developer or know languages like Java or Python. The CKS is an infrastructure and operational security exam. However, you must be very comfortable with Linux command-line tools, editing YAML files, and using kubectl.
8. Does the exam focus on a specific cloud provider like AWS or Azure?
No, the CKS exam is completely vendor-neutral. You will be tested on a standard, “vanilla” Kubernetes cluster running on Linux. The security principles and tools you learn will apply equally whether you use Amazon EKS, Azure AKS, Google GKE, or your own on-premise servers.
Conclusion
Securing Kubernetes is no longer an afterthought—it is a critical requirement for every modern business. The Certified Kubernetes Security Specialist (CKS) is more than just a piece of paper; it is a rigorous, undeniable proof that you have the practical skills to defend complex, cloud-native infrastructures against real-world threats. Whether you are looking to pivot into DevSecOps, solidify your position as an SRE, or simply become the go-to Kubernetes expert in your organization, the CKS is the catalyst you need. The journey will be challenging, and it will test your limits, but the career outcomes are profoundly worth it.
The preparation tips shared here are very useful, especially for candidates planning a structured study approach. It gives a clear direction to start.